MrPentester helped us when our website was under continuos attack and we were demanded ransom as payment, but MrPentester team took the challenge and restored our services within 3 hours and eliminated all loopholes within a day. Highly recommended.
Managed Security Operations Center(SOC)
Concerned about cyberattacks? SOC-as-a-service for you to keep attacks away!
Data security is a critical concern among enterprise businesses as cyberattacks are increasingly rapid and widespread. Throughout the digital sphere attacks have been persisting with great frequency despite use of high-tech. SOC-as-a-service is used to keep these types of attacks away from the organizations.!
Talk To a Security Expert
We Will Help You To Choose The Best Plan!
Managed Security Operations Center(SOC)
SOC-as-a-service with 360 degree approach to find and fix critical data leaks or potential threat in your infrastructure and across.
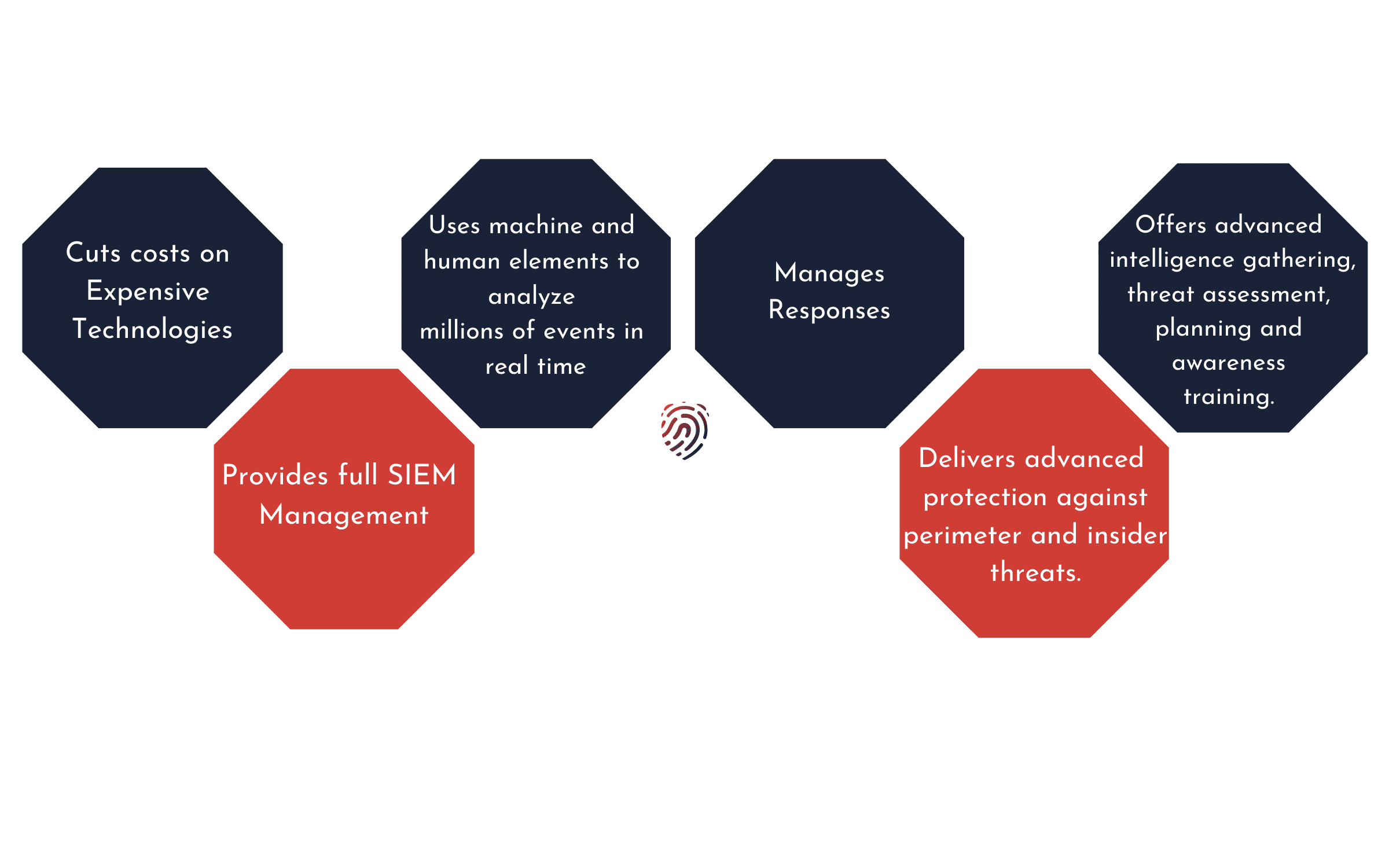
Approach for Managed Security Operations Center(SOC)
Cut expensive technological costs
With SOC-as-a-service, companies can cut down on the expenses typically associated with cybersecurity and receive advanced protection from cyber intrusions. SOC enables you to allocate more resources for your company ideas, focusing on promoting your own products and services, leaving security up to trained professionals.
Right Approach
Our team brainstorms for solutions and uses the best possible methodologies for tracking down critical data and later assisting in mitigating them. We keep upgrading ourselves constantly to remain advanced and our approach is designed to upgrade security across your information infra.
Highly Affordable
Even a small organization can hire SOC-as-a-service, and engineers who run the third party service can handle the important aspects of security enforcement. We offer plug n play pricing and flexible charges.
Partners forever
We believe in creating everlasting relationships of unbreakable security bond, our primary focus is upon securing your infra, given our passion towards the domain and commitment, any variables are secondary to it. We believe in going long way!
- Cut expensive technological costs
Cut expensive technological costs
With SOC-as-a-service, companies can cut down on the expenses typically associated with cybersecurity and receive advanced protection from cyber intrusions. SOC enables you to allocate more resources for your company ideas, focusing on promoting your own products and services, leaving security up to trained professionals. - Right Approach
Right Approach
Our team brainstorms for solutions and uses the best possible methodologies for tracking down critical data and later assisting in mitigating them. We keep upgrading ourselves constantly to remain advanced and our approach is designed to upgrade security across your information infra. - Highly Affordable
Highly Affordable
Even a small organization can hire SOC-as-a-service, and engineers who run the third party service can handle the important aspects of security enforcement. We offer plug n play pricing and flexible charges. - Partners forever
Partners forever
We believe in creating everlasting relationships of unbreakable security bond, our primary focus is upon securing your infra, given our passion towards the domain and commitment, any variables are secondary to it. We believe in going long way!
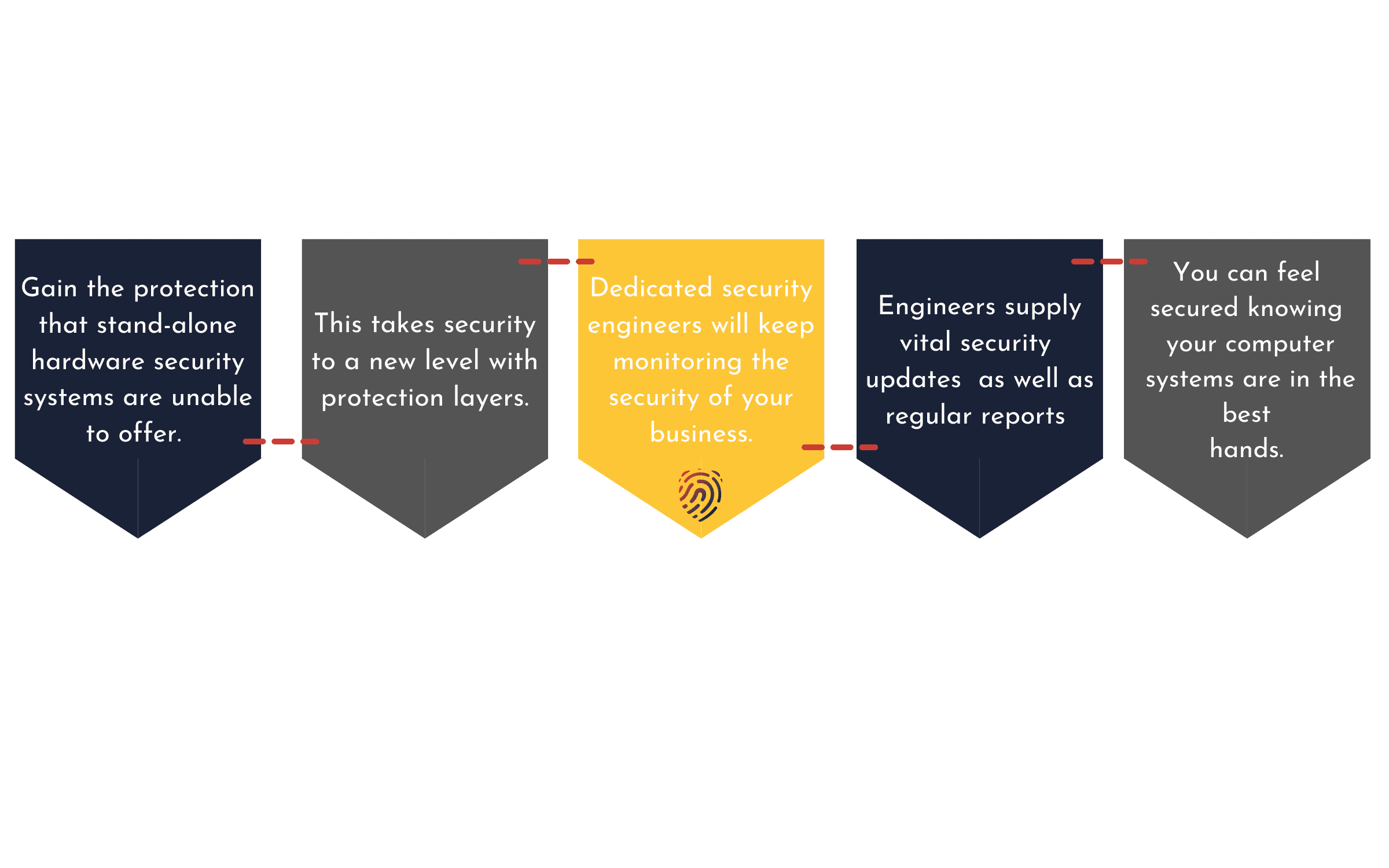
How we differ
MrPentester's SOC-as-a-service is not just a set of checklist to run through or an excel sheet to work with, but an exclusive experience to safeguard your business reputation & information infra!
- Identifying publicly available sensitive user data.
- Efficient approach & advanced methodologies to protect your Information Infrastructure
- Transparent visibility on the project status & updates.
- High quality, fully segregated and top standard report quality to present to the CXO.
- Integrated secure coding campaign for developers.
- Detailed & simplified reports for all the re-assessments with Track.
- The service allows companies to rank the importance of layers of data and determine the severity of threats that surface on the radars of computer networks.

More about our Solutions!